Stay away from Cloudflare
Published on 2017-12-20.
Cloudflare has become one of the fastest growing DNS and CDN hosters on the Internet delivering some of the best DNS speeds worldwide, but if you value customers or visitors to your website you maybe need reconsider using Cloudflare.
Cloudflare delivers great DNS speeds worldwide and they have a really well designed control panel for managing DNS hosting, combine that with a premium free service and you get a powerful and very attracting DNS hosting solution for bloggers, webshop owners, and anyone else who owns a website. However, what most people overlook is that Cloudflare, in the name of security, every day blocks millions of valid users from visiting the websites that Cloudflare has registered in their hosting service.
In the control panel for DNS setup you have an option called "Firewall", and within that option there is a setting called "Security level".
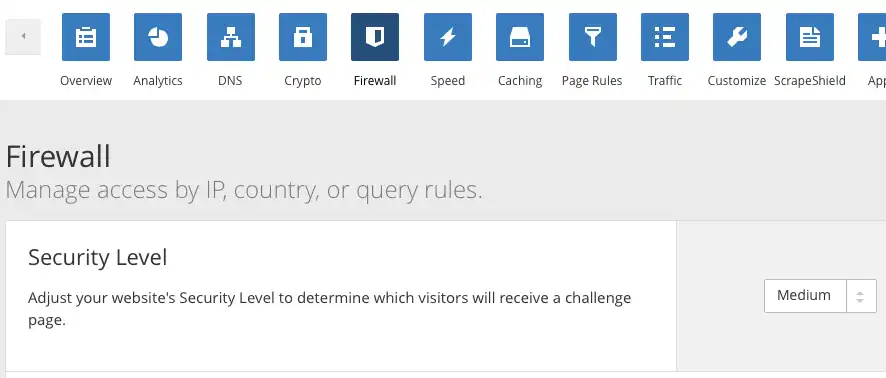
By default it is set to "Medium", which means that a lot of people will be blocked from your website by a very annoying and time consuming CAPTCHA. And the problem with this option is that it cannot be disabled in the free service. You actually has to pay for the Enterprise edition, which is more that 200 dollars a month per domain, in order to disable the feature. Even if you set the setting to the lowest available value in the free service, which is Essentially off, many of your visitors will still be blocked.
In case you haven't seen it, this is how it looks:
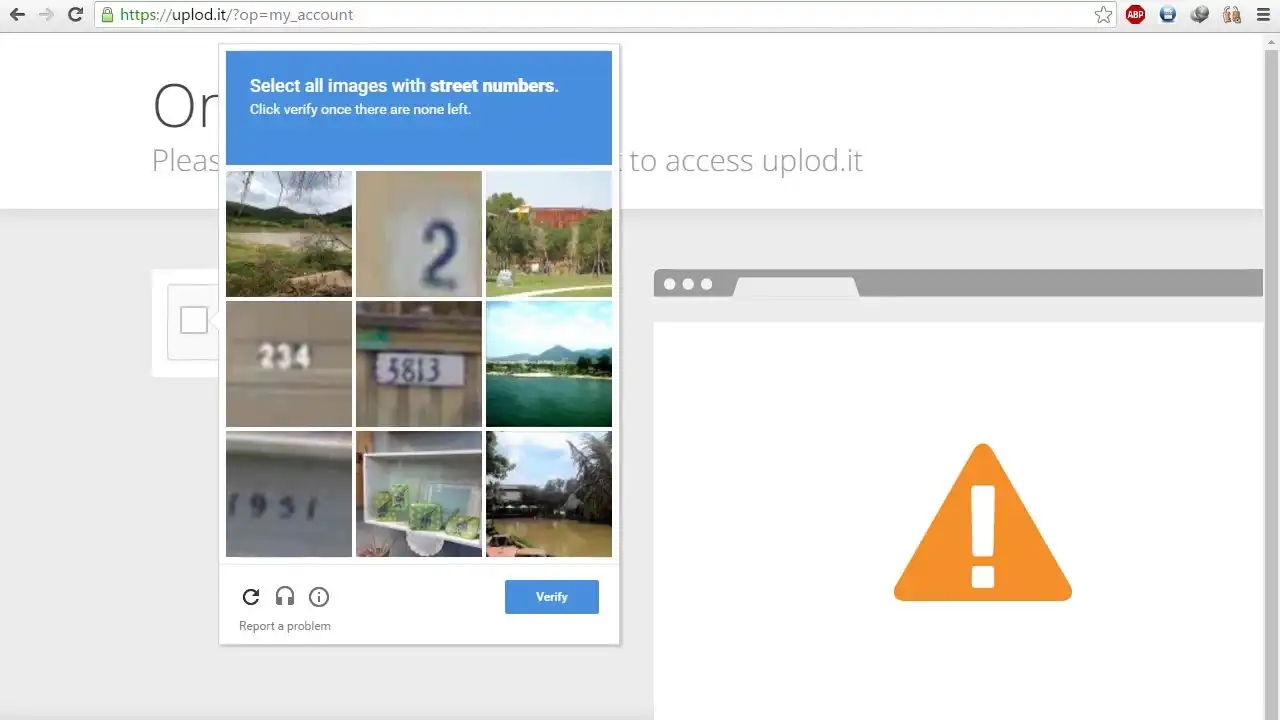
The CAPTCHA may look harmless enough, but often it gets repeated several times displaying different puzzles to solve. Many times a fadeout effect has been inserted when you click on a picture and the picture takes about 3-4 seconds before it vanishes only to be replaced by yet another picture.
The process is extremely annoying and many people will simply leave your website in frustration.
The demand for privacy on the Internet is growing rapidly and every day more and more people are signing up for VPN services around the world. These services are often blocked by default by Cloudflare and this is a serious problem.
Here's a video example on how annoying it can be if you're using a VPN service or an anti-tracking plug-in for Firefox:
Nobody wants to fill out an annoying CAPTCHA just to visit your website, no matter what you have to offer. And just as rapidly growing as Cloudflare is, just as rapidly do people boycott websites that are using the Cloudflare DNS hosting solution.
Cloudflare as MITM (man-in-the-middle)
Another very serious problem with Cloudflare is that they act as a MITM (man-in-the-middle) with their CDN (content delivery network) service in which they, amongst other things, cache your website content and display that to your visitors. If you're running a normal website, like a blog, many times people will never actually visit your website, they'll just get the content from Cloudflare. However, this is not the serious problem, the serious problem is that they provide SSL connections for all who use their service in a way that they become a man-in-the-middle. Your connection is only really encrypted up until the Cloudflare servers, after that the connection can simply be clear text. The connection is encrypted between the browser and Cloudflare, and between Cloudflare and the website if the website has a SSL certificate, but the communication in-between remains completely visible to Cloudflare.
You can check this by going to any website that uses a Cloudflare's SSL connection. Check the certificate for the website. You'll notice that it's a Cloudflare certificate and not a certificate for the website you're actually visiting.
How does this pose a problem?
Imagine B as your browser and S as the webserver. In a normal communication flow it would look like this:
B <---> S
When you visit a website with a SSL connection, your browser (B) checks the encryption certificate and if it validates, an encrypted connection is established between your browser (B) and the webserver (S). Now imagine that we setup another computer in-between your browser and the webserver.
B <---> C <---> S
In this setup both the computer in the middle (C) and the webserver has a SSL certificate. When your browser requests an encrypted connection to the website, it gets the certificate from the computer in the middle, in this case Cloudflare, then an encrypted communication is established between these two. Then the computer in the middle does the same with the webserver, and an encrypted connection is established between the computer in the middle and the webserver. However, the computer in the middle now sees everthing.
So do you really want Cloudflare to snatch the communication between your website and your visitors or customers? Cloudflare will be able to see everything even when you have a SSL certificate running on your webserver.
You need to understand that users, the visitors to your website, are being mislead by the padlock icon that falsely state that the connection to your website is secure. Users believe, when they see the padlock icon, that the have a secure end-to-end tunnel to your website, while they unwittingly have a tunnel to Cloudflare, who sees all the trafic before it reaches your website.
That is NOT ok!
It means that sensitive data is being disclosed to Cloudflare without the consent or knowledge of your visitors.
Alternative solutions
This list has been put together by "joepie91" on Hacker News
If you're looking for DDoS mitigation, use basically any of the providers that offer it on a network level - it's really not necessary to have access to HTTP traffic to mitigate attacks. Also, don't run Apache - it's notoriously vulnerable to various low-bandwidth attacks.
A non-exhaustive list of "real" mitigation providers (note that I am not making any particular recommendations):
- Voxility
- X4B.net
- Akamai (formerly Prolexic)
- Level3 (formerly Black Lotus)
- Psychz Networks
- CNServers
- Sharktech
- OVH (not as a separate service, but their entire network is covered)
You'll want to avoid anything HTTP-specific (as it will be prone to the same privacy issues as Cloudflare), and opt for layer 3/4 mitigation only. Another option, if you're running at a larger scale, is to purchase mitigation appliances and just set up your own mitigation infrastructure. This will not be cheap and require some serious connectivity, but beyond a certain point it'll be more cost-effective. If you're looking for a WAF, run one on your own backend server(s) and/or loadbalancer(s). There's no benefit to doing this remotely, really. Even something relatively simple like ModSecurity will cover a wide array of problems.
If you're looking for DNS hosting: plenty of options. Many providers offer it for free if you host with them, Hurricane Electric offers it for free regardless of where you are hosted, and if you need an SLA, there's Rage4 and Route 53. Pretty much every DNS hosting provider uses anycast.
If you're looking for magic SSL/TLS: Use Caddy, which is a HTTP server that will automatically set up and renew certificates for you through Let's Encrypt, as well as greatly simplifying TLS configuration. It's essentially zero-effort.
Trying to outsource this to a third party (like Cloudflare's "Universal SSL/TLS") defeats the point - it means that the third party can see all of your traffic, all the while providing a false sense of security to your users. The users see the padlock, but their traffic is not secured end-to-end.
In short: the only correct place to terminate TLS is on your own servers!
Detecting Cloudflare
This Firefox plug-in detects Cloudflare and lets you know: Detect Cloudflare plug-in